- Pro
- Security
SHA-1 is removed entirely as Tor adopts a stronger authentication method
Comments (0) ()When you purchase through links on our site, we may earn an affiliate commission. Here’s how it works.
 (Image credit: bleepingcomputer)
(Image credit: bleepingcomputer)
- Tor dumps tor1 and moves to a stronger, research-driven relay encryption system
- CGO introduces modern protections that block tagging attacks across the network
- Wide-block encryption makes modified cells unrecoverable and stops predictable interception attempts
Tor has introduced a new relay encryption system called Counter Galois Onion (CGO) to replace the older tor1 algorithm.
The change is intended to make the network more resilient against modern interception techniques that could compromise user privacy.
- Amazon Black Friday deals are live: here are our picks!
CGO is built on a Rugged Pseudorandom Permutation called UIV+, designed by cryptography researchers to meet rigorous security requirements.
You may like-
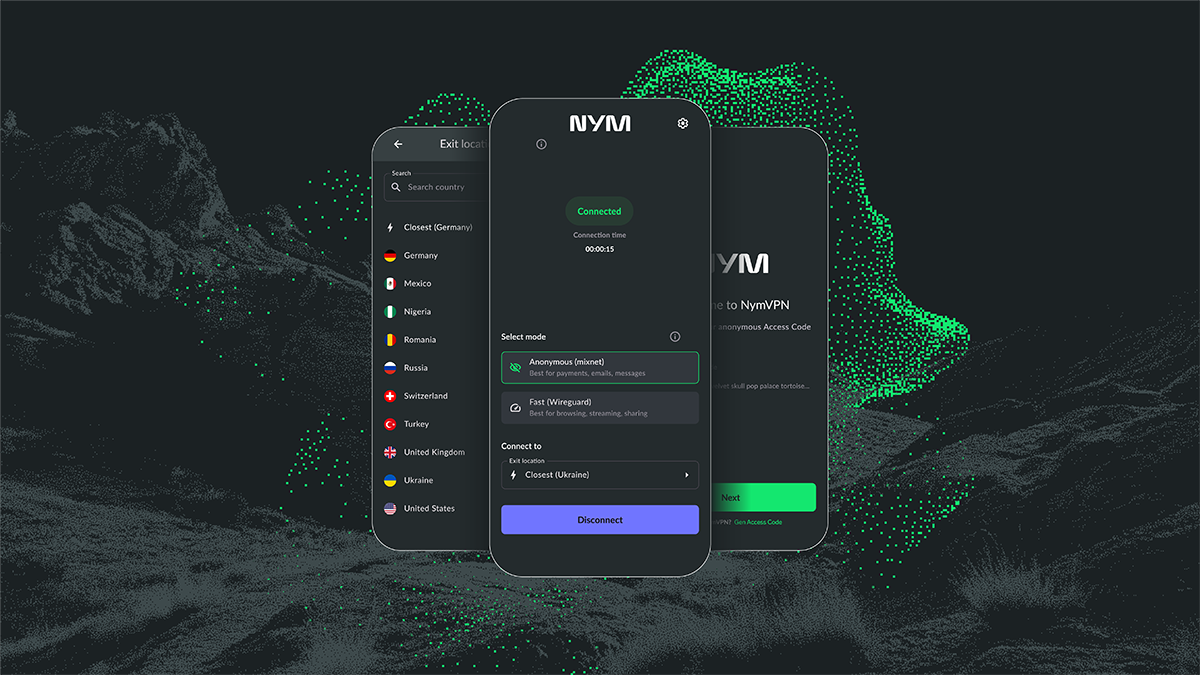
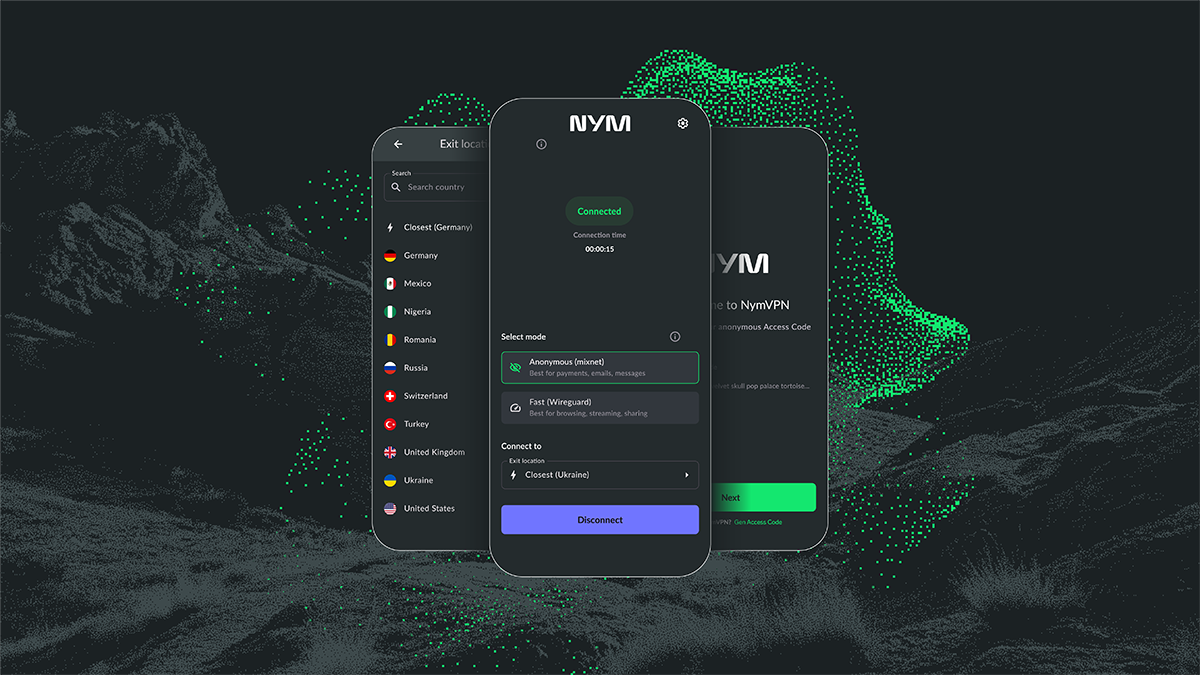 NymVPN boosts its censorship-unlocking power with new features
NymVPN boosts its censorship-unlocking power with new features
-
 Windscribe VPN just made WireGuard even more quantum-resistant
Windscribe VPN just made WireGuard even more quantum-resistant
-
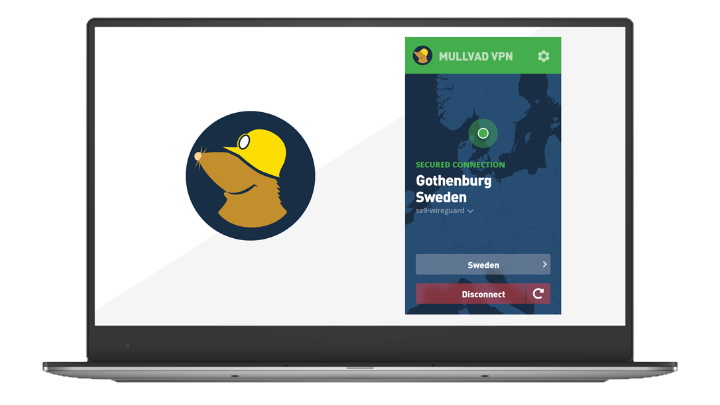
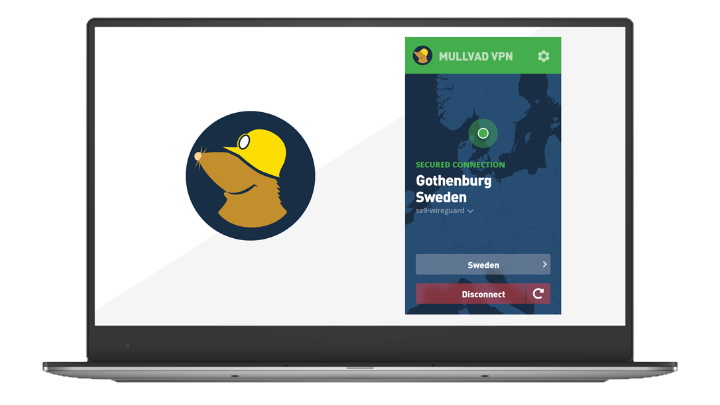 Now you see me, now you don’t – Mullvad introduces QUIC to disguise WireGuard traffic
Now you see me, now you don’t – Mullvad introduces QUIC to disguise WireGuard traffic
Addressing vulnerabilities in tor1
Tor reports this system has been verified for tagging resistance, forward secrecy, longer authentication tags, and efficient operation without adding significant bandwidth overhead.
The previous tor1 relay encryption had multiple weaknesses by modern standards, mainly as it relied on AES-CTR encryption without hop-by-hop authentication, allowing a potential adversary controlling relays to modify traffic predictably, creating tagging attack opportunities.
It also reused AES keys throughout a circuit, offering only partial forward secrecy, and used a 4-byte SHA-1 digest for authentication, giving a small chance that a forged cell could go undetected.
Tor maintains while only the first issue is critical, all three represent areas requiring improvement as cryptography standards evolve.
Are you a pro? Subscribe to our newsletterContact me with news and offers from other Future brandsReceive email from us on behalf of our trusted partners or sponsorsBy submitting your information you agree to the Terms & Conditions and Privacy Policy and are aged 16 or over.CGO introduces wide-block encryption and tag chaining, which renders modified cells and future traffic unrecoverable, effectively blocking tagging attacks.
The keys are updated after each cell to prevent decryption of past traffic even if current keys are exposed.
SHA-1 has been removed entirely and replaced with a 16-byte authenticator, enhancing overall security.
You may like-
 NymVPN boosts its censorship-unlocking power with new features
NymVPN boosts its censorship-unlocking power with new features
-
 Windscribe VPN just made WireGuard even more quantum-resistant
Windscribe VPN just made WireGuard even more quantum-resistant
-
 Now you see me, now you don’t – Mullvad introduces QUIC to disguise WireGuard traffic
Now you see me, now you don’t – Mullvad introduces QUIC to disguise WireGuard traffic
Circuit integrity is strengthened by chaining encrypted tags and nonces across cells, making any tampering immediately detectable.
Tor emphasizes these measures address previous weaknesses while maintaining reasonable performance.
The CGO system is being integrated into both the C Tor implementation and the Rust-based Arti client.
The feature is currently experimental, with additional work planned for onion service negotiation and performance optimization.
Tor Browser users do not need to take any action to benefit from CGO, as the update will apply automatically once the system is fully deployed.
A timeline for when CGO will become the default encryption method has not yet been announced.
Via BleepingComputer
Follow TechRadar on Google News and add us as a preferred source to get our expert news, reviews, and opinion in your feeds. Make sure to click the Follow button!
And of course you can also follow TechRadar on TikTok for news, reviews, unboxings in video form, and get regular updates from us on WhatsApp too.
 Efosa UdinmwenFreelance Journalist
Efosa UdinmwenFreelance JournalistEfosa has been writing about technology for over 7 years, initially driven by curiosity but now fueled by a strong passion for the field. He holds both a Master's and a PhD in sciences, which provided him with a solid foundation in analytical thinking.
You must confirm your public display name before commenting
Please logout and then login again, you will then be prompted to enter your display name.
Logout Read more NymVPN boosts its censorship-unlocking power with new features
NymVPN boosts its censorship-unlocking power with new features
 Windscribe VPN just made WireGuard even more quantum-resistant
Windscribe VPN just made WireGuard even more quantum-resistant
 Now you see me, now you don’t – Mullvad introduces QUIC to disguise WireGuard traffic
Now you see me, now you don’t – Mullvad introduces QUIC to disguise WireGuard traffic
 The Tor Project quietly launches a beta Android VPN – and looks for testers
The Tor Project quietly launches a beta Android VPN – and looks for testers
 Mullvad VPN adds ultra-fast obfuscation to beat WireGuard blocking
Mullvad VPN adds ultra-fast obfuscation to beat WireGuard blocking
 Mobile Mullvad VPN users gain QUIC-enabled censorship bypass
Latest in Security
Mobile Mullvad VPN users gain QUIC-enabled censorship bypass
Latest in Security
 Take extra care shopping for Black Friday deals - experts find thousands of fake websites looking to steal your details
Take extra care shopping for Black Friday deals - experts find thousands of fake websites looking to steal your details
 Microsoft Teams guest access could let hackers bypass some critical security protections
Microsoft Teams guest access could let hackers bypass some critical security protections
 Many of us aren't confident we could spot a fake website this Black Friday - so be on your guard
Many of us aren't confident we could spot a fake website this Black Friday - so be on your guard
 Excited for your Christmas bonus? So are scammers - so make sure you check your emails carefully
Excited for your Christmas bonus? So are scammers - so make sure you check your emails carefully
 Malicious LLMs are letting even unskilled hackers to craft dangerous new malware
Malicious LLMs are letting even unskilled hackers to craft dangerous new malware
 Multiple London councils affected by apparent cyberattack
Latest in News
Multiple London councils affected by apparent cyberattack
Latest in News
 LaLiga football streaming behind Cloudflare weekend outages as Spaniards turn to Proton VPN
LaLiga football streaming behind Cloudflare weekend outages as Spaniards turn to Proton VPN
 Missouri's search for VPNs lifts off as the first day of age verification arrives
Missouri's search for VPNs lifts off as the first day of age verification arrives
 If you want a huge battery in your phone, try the upcoming OnePlus 15R
If you want a huge battery in your phone, try the upcoming OnePlus 15R
 It looks as though we shouldn't expect big upgrades from the Galaxy S26
It looks as though we shouldn't expect big upgrades from the Galaxy S26
 OpenAI reveals ChatGPT’s most popular features
OpenAI reveals ChatGPT’s most popular features
 Quordle hints and answers for Monday, December 1 (game #1407)
LATEST ARTICLES
Quordle hints and answers for Monday, December 1 (game #1407)
LATEST ARTICLES- 1Tor adds another layer to the onion with a new relay encryption algorithm - boosting resilience and security across the board
- 2Scared you'll delete important work files? This backup-focused cloud storage could ease your fears this Cyber Monday
- 3Dell says businesses still aren't moving to Windows 11 fast enough - PC maker says sales will be flat as many stick with Windows 10
- 4Cloud storage is a vital part of business - and this IONOS plan will cost you less than a pizza this Cyber Monday
- 5LaLiga football streaming behind Cloudflare weekend outages as Spaniards turn to Proton VPN


